12/3/2024
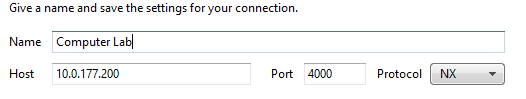
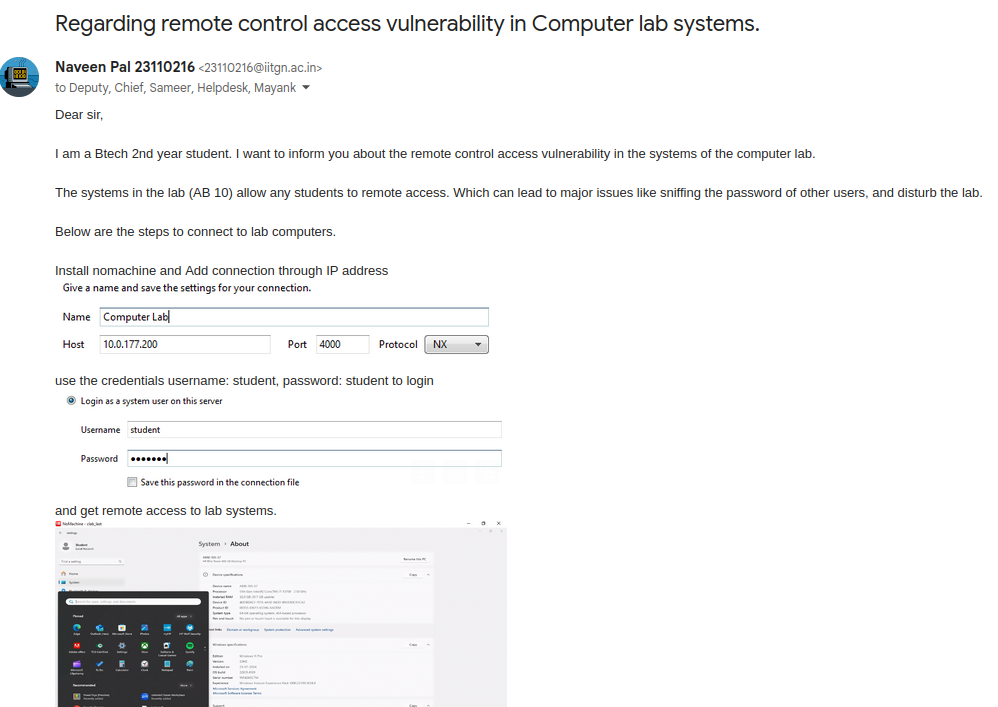
During a regular session in the computer lab, I noticed NoMachine installed on the systems. After researching (basically googling) the software, I learned that NoMachine is a remote desktop solution operating on port 4000 using the NX protocol.
Time to exploit
- Setup
- Installed NoMachine on my laptop
- Attempted connection to lab computer’s IP
- Authentication
- System prompted for credentials
- Default student credentials were accepted
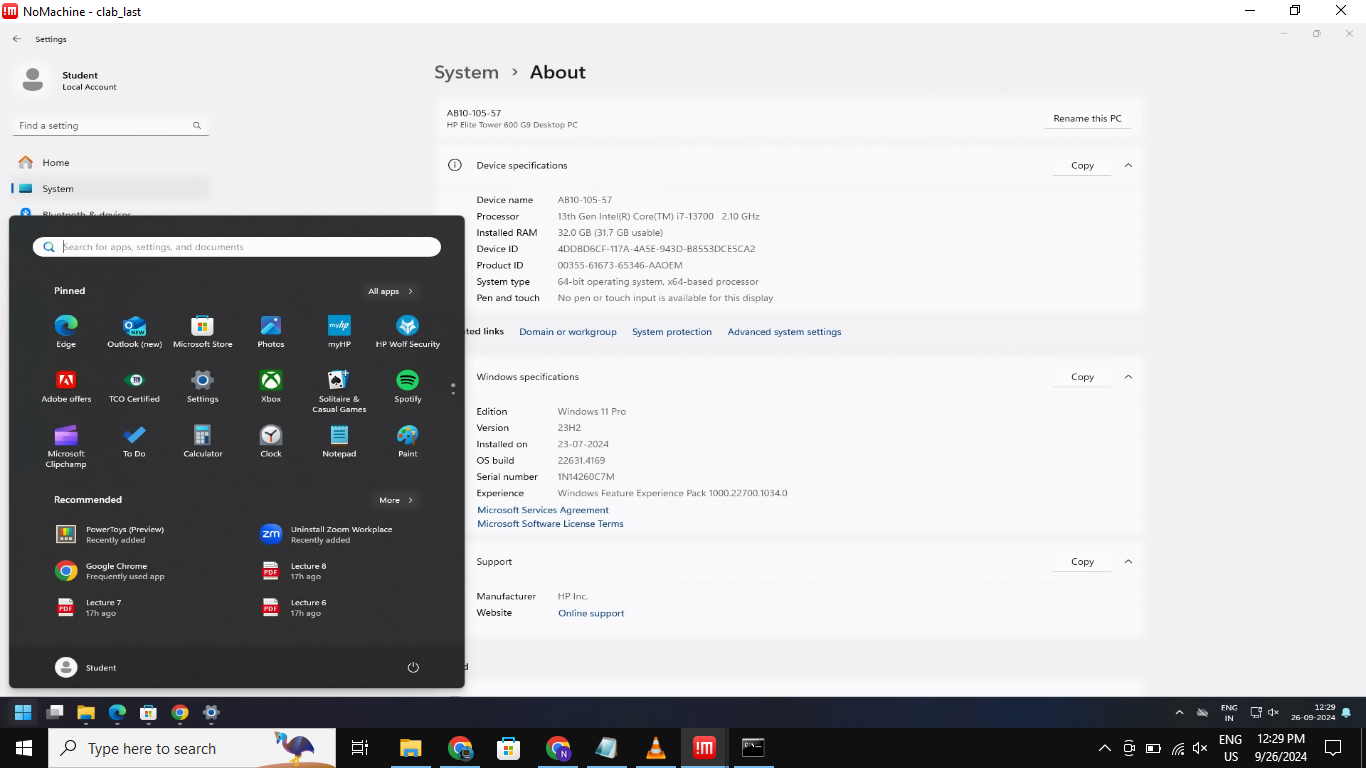
- Successful Access
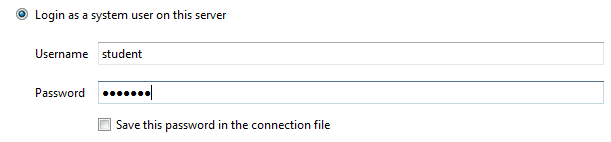
- Gained non-administrative remote access
- Full user-level control achieved
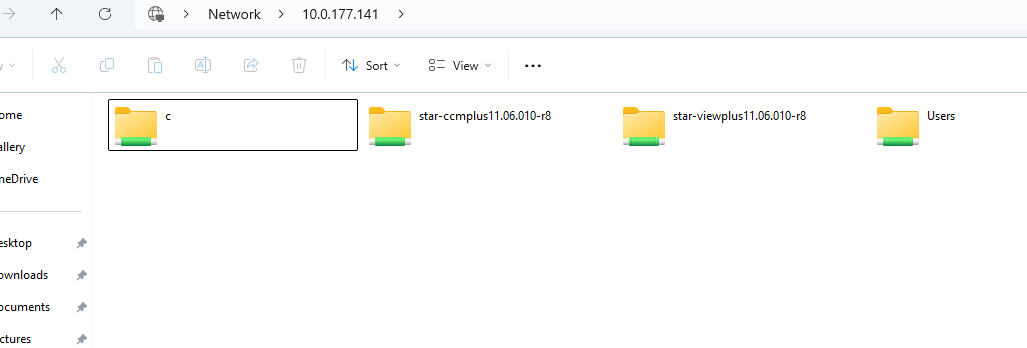
SMB Vulnerability
A second vulnerability was discovered involving unrestricted access to system files through SMB (Server Message Block) protocol.
Got to know via Chandrabhan Patel, who identified the Remote File Inclusion vulnerability.
Vulnerabilities were promptly reported to the ISTF and the issues were acknowledged and No machine is no more installed in the lab systems.
Ah so it was possible to cheat during lab exams?
While this was a natural concern, the faculty already had preventive measures in place, including disabling external connections during examinations. When the connection get stop it doesn’t just the internet it stop the local communication between devices.
Happy Hacking!